ProvenCore: The essence of Trust
“Our vision is to instill absolute trust in the Internet of Things, and ProvenCore is a testament to our dedication.”
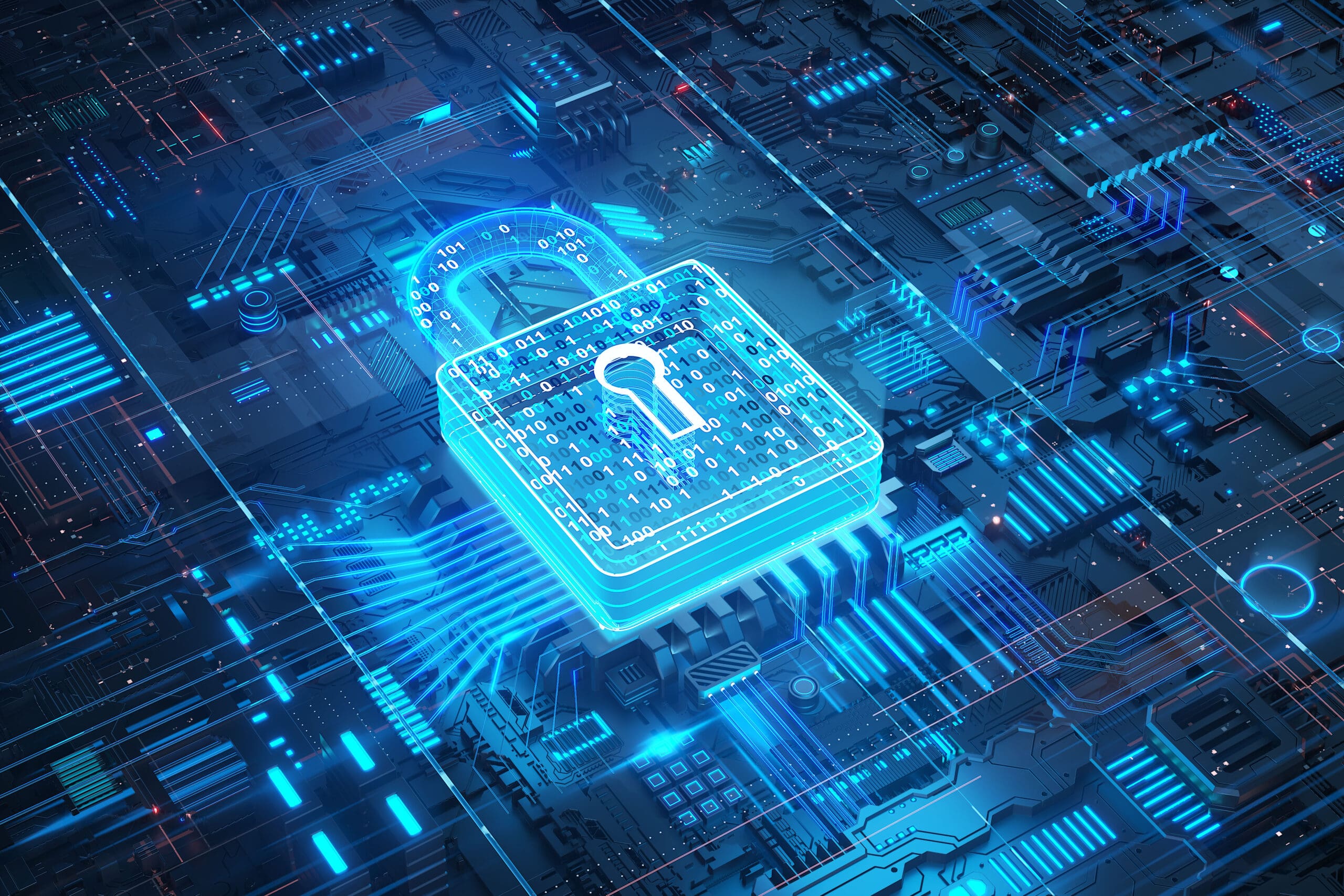
At ProvenRun, we firmly believe that trust is the cornerstone of any successful IoT ecosystem. With our unwavering commitment to realizing complete trust in IoT, we introduce ProvenCore: an advanced secure Operating System/Trusted Execution Environment (TEE) meticulously crafted to deliver unmatched security for your IoT devices. By focusing on trust from the ground up, we enable businesses, organizations, and individuals to operate with confidence, knowing that their embedded devices are safeguarded against emerging remote threats.
ProvenCore | The Essence of Trust.
ProvenCore stands at the forefront of secure Operating Systems, serving as the nucleus of a device’s Trusted Computing Base. Developed using deductive formal methods, ProvenCore is a Trusted Execution Environment (TEE) designed to provide unparalleled security for microprocessors and host critical security services.
Building Resilience | ProvenCore's Proactive Approach to IoT Security.
With ProvenCore, we prioritize trustworthy design to ensure uncompromising security. Our commitment to formal methods means that every aspect of ProvenCore has been meticulously analyzed, verified, and proven. By adhering to this rigorous approach, we eliminate exploitable vulnerabilities and minimize the risk of remote attacks.

Unlocking Trust | Key Features of ProvenCore
Security

Ultra Secure Containers
Certifiable

Autonomous Secure OS
GlobalPlatform Compliant
Trusted Application Catalog

Software Development Kit
Scalable and Modular Architecture
Broad Hardware Support:
ProvenCore offers a strong value proposition compared to other Trusted Execution Environments (TEEs) available on the market. Here are some key advantages of ProvenCore:
Unmatched Security

Future-Proofing Your Investments
Seamless Integration and Interoperability
Accelerated Time-to-Market

Total Cost of Ownership

ProvenRun's Expertise and Support
Choose ProvenCore | Choose Trust.
ProvenCore empowers you to build a secure and trusted IoT landscape. With our Trusted Execution Environment at the core of your devices, you can unlock new levels of protection and establish trust among your customers and stakeholders. Experience the Power of ProvenCore’s Trusted Execution Environment today. Contact us to get started on your journey towards a more secure IoT ecosystem.